How the OpenClaw GitHub Phishing Attack Actually Worked - And How to Defend Against It
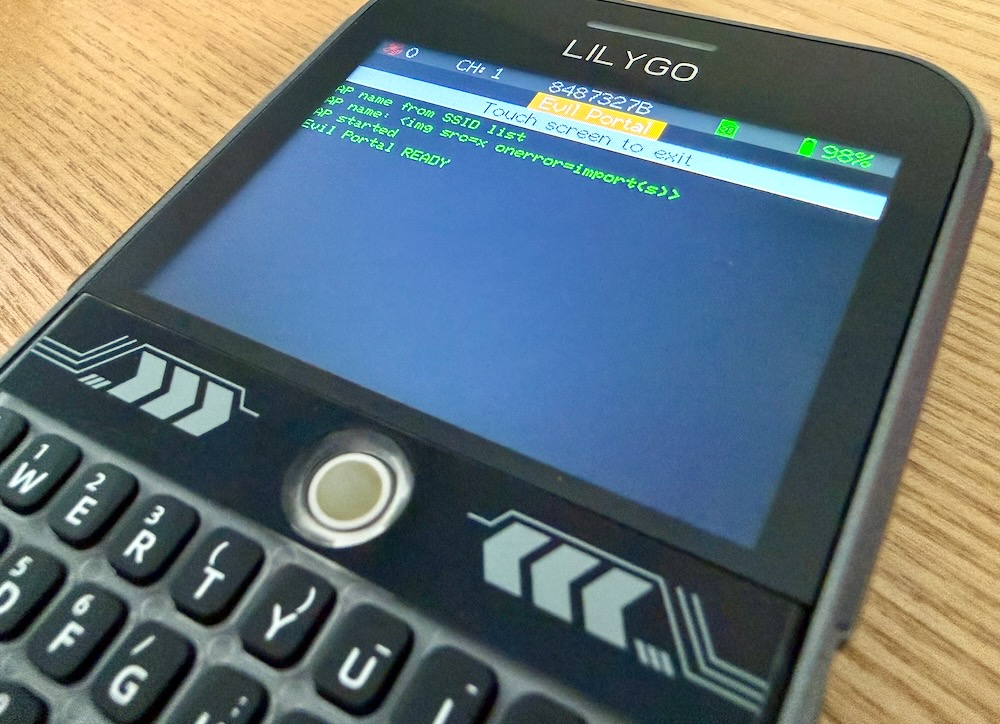
In early 2026, a phishing campaign targeted developers who had starred the OpenClaw repository on GitHub. No zero-days. No CVEs. Just precise social engineering layered on top of trusted infrastruc...

Source: DEV Community
In early 2026, a phishing campaign targeted developers who had starred the OpenClaw repository on GitHub. No zero-days. No CVEs. Just precise social engineering layered on top of trusted infrastructure - and a JavaScript wallet drainer that wiped its own evidence. This article covers exactly three things: how the attack unfolded, what the attacker did technically, and what you can do to protect yourself. How the Attack Unfolded Building a Target List from GitHub Stars The attackers did not send a generic blast. They enumerated users who had publicly starred OpenClaw-related repositories on GitHub. This turned a mass phishing attempt into something that felt personal - a message about a project you had already shown interest in. Attackers started by enumerating users who had publicly starred OpenClaw repositories, built a curated target list from that data, and then used it to send targeted @mentions in GitHub issue threads. Abusing GitHub's Notification System Fake GitHub accounts were